Introduction
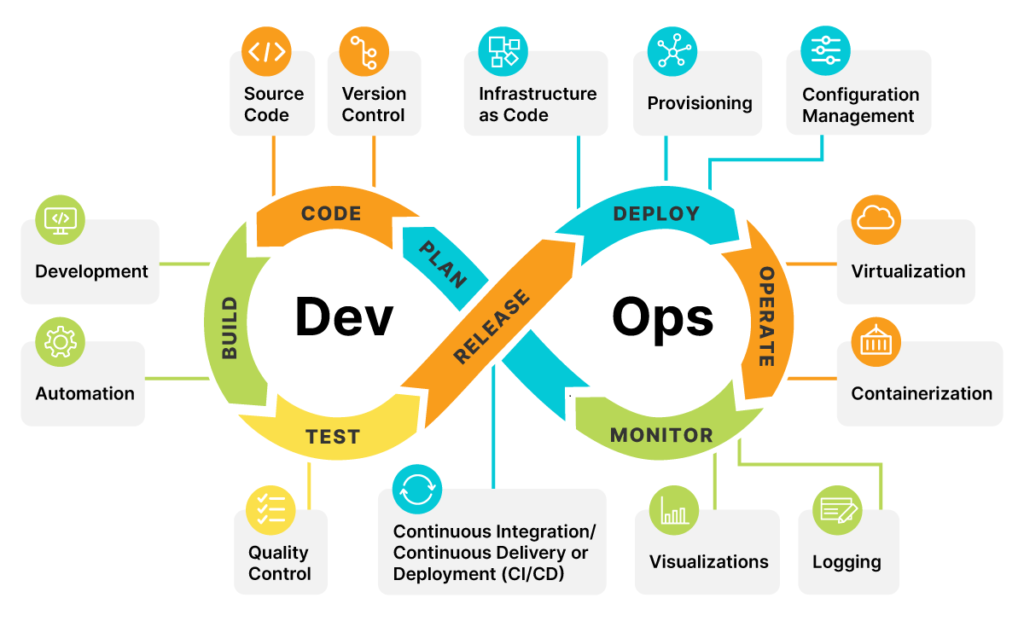
As organizations rapidly adopt cloud computing, microservices architecture, and containerized applications, DevOps teams are under increasing pressure to deliver software faster while maintaining high levels of reliability and security.
Traditional security approaches, where security checks occur only after development, are no longer effective in modern cloud-native environments. Instead, organizations must adopt DevSecOps, a strategy that integrates security into every stage of the software development lifecycle (SDLC) and CI/CD pipelines.
DevSecOps enables organizations to embed security automation, vulnerability scanning, compliance checks, and threat detection directly into their development workflows. This approach helps identify vulnerabilities early, reduce security risks, and ensure applications remain secure throughout deployment.
In this blog, we explore DevSecOps for cloud infrastructure, the importance of integrating security into CI/CD pipelines, and practical strategies DevOps teams can implement to build secure and scalable cloud environments.
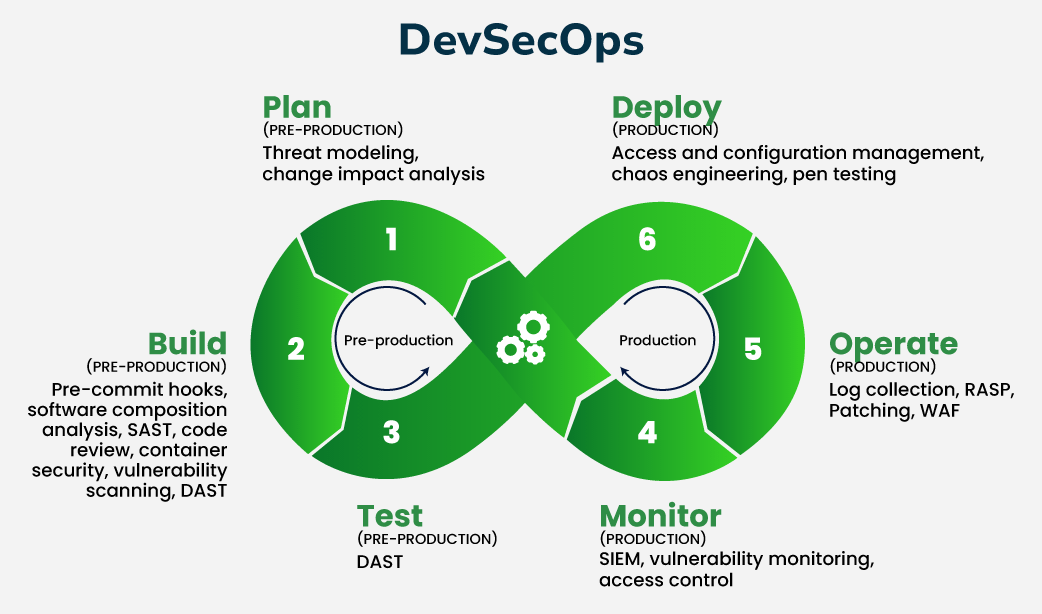
What is DevSecOps?
DevSecOps stands for Development, Security, and Operations. It is a modern approach that integrates security practices directly into DevOps workflows rather than treating security as a separate process.
The primary objective of DevSecOps is to ensure that security becomes a shared responsibility across development, operations, and security teams.
Key principles of DevSecOps include:
-
Security automation within CI/CD pipelines
-
Continuous vulnerability scanning
-
Infrastructure as Code (IaC) security checks
-
Secure container and Kubernetes deployments
-
Compliance monitoring and policy enforcement
By implementing DevSecOps practices, organizations can achieve faster software delivery while maintaining strong cybersecurity posture and regulatory compliance.
Why DevSecOps is Critical for Cloud Infrastructure
Cloud infrastructure environments such as AWS, Microsoft Azure, and Google Cloud Platform (GCP) provide flexibility and scalability, but they also introduce new security challenges.
Without integrated security practices, cloud environments may suffer from:
-
Misconfigured cloud resources
-
Vulnerable container images
-
Insecure APIs
-
Weak access controls
-
Unpatched software dependencies
DevSecOps ensures that security checks are embedded into the CI/CD pipeline, enabling teams to detect and fix vulnerabilities before applications reach production.
Security Risks in Traditional DevOps Pipelines
Before adopting DevSecOps, many organizations rely on traditional DevOps pipelines that focus mainly on speed and automation.
Common risks include:
1. Late Security Testing
Security testing performed only during final stages of development often leads to delayed vulnerability detection.
Fixing vulnerabilities late in the development cycle increases both cost and risk.
2. Insecure Infrastructure as Code (IaC)
Cloud infrastructure is commonly deployed using Infrastructure as Code tools such as Terraform, CloudFormation, and Kubernetes manifests.
If IaC templates contain misconfigurations, they can expose cloud resources to attackers.
3. Vulnerable Containers and Images
Containers accelerate application deployment but may include outdated libraries, vulnerable dependencies, or insecure configurations.
Without proper container security scanning, these vulnerabilities can enter production environments.
4. Lack of Continuous Monitoring
Traditional DevOps models often lack continuous security monitoring, making it difficult to detect threats and anomalies in real time.
Integrating Security into CI/CD Pipelines
DevSecOps focuses on embedding security across the entire Continuous Integration and Continuous Deployment (CI/CD) pipeline.
1. Secure Code Development
Security should begin during the coding phase.
Best practices include:
-
Secure coding standards
-
Code review processes
-
Static Application Security Testing (SAST)
-
Dependency vulnerability scanning
Tools such as SonarQube, Snyk, and Checkmarx help identify vulnerabilities during development.
2. Automated Security Testing
Automation plays a critical role in DevSecOps. CI/CD pipelines should include automated security testing tools such as:
-
Static Application Security Testing (SAST)
-
Dynamic Application Security Testing (DAST)
-
Software Composition Analysis (SCA)
These tools continuously scan applications for vulnerabilities and security flaws.
3. Infrastructure as Code Security Scanning
Since cloud infrastructure is deployed through code, it must be validated before deployment.
IaC security scanning tools can detect:
-
Open storage buckets
-
Weak access control policies
-
Misconfigured cloud services
Tools commonly used include:
-
Terraform security scanners
-
AWS Config
-
Checkov
-
Bridgecrew
4. Container and Kubernetes Security
Modern applications frequently run on Docker containers and Kubernetes clusters.
DevSecOps pipelines should include container security checks such as:
-
Container image scanning
-
Kubernetes configuration validation
-
Runtime security monitoring
Tools like Aqua Security, Prisma Cloud, and Trivy help secure container environments.
5. Continuous Compliance Monitoring
Organizations must ensure compliance with security standards including:
-
ISO 27001
-
SOC 2
-
NIST Cybersecurity Framework
-
GDPR
-
HIPAA
DevSecOps integrates compliance checks directly into CI/CD pipelines, enabling continuous compliance monitoring.
Best Practices for Implementing DevSecOps in Cloud Infrastructure
Shift Security Left
The “Shift Left” approach means integrating security early in the development lifecycle.
By detecting vulnerabilities earlier, organizations reduce remediation costs and improve application security.
Implement Zero Trust Security
Zero Trust architecture assumes that no user or system should be trusted by default.
Key components include:
-
Identity and Access Management (IAM)
-
Multi-Factor Authentication (MFA)
-
Network segmentation
-
Continuous authentication
Use Security Automation
Manual security checks slow down development. Automation allows DevOps teams to perform continuous security testing and vulnerability detection without impacting release cycles.
Monitor Cloud Infrastructure Continuously
Cloud security monitoring tools help detect:
-
Unauthorized access attempts
-
Suspicious activity
-
Configuration changes
-
Compliance violations
Continuous monitoring ensures that cloud environments remain secure after deployment.
Benefits of DevSecOps for Cloud Environments
Organizations that implement DevSecOps gain several advantages:
✔ Faster and more secure software releases
✔ Early detection of vulnerabilities
✔ Reduced security risks in cloud environments
✔ Improved compliance with security regulations
✔ Better collaboration between development, security, and operations teams
✔ Enhanced protection against cyber threats
DevSecOps ultimately helps organizations achieve secure cloud infrastructure and resilient application environments.
How Gigahertz Consultants Can Help
At Gigahertz Consultants, we help organizations implement secure DevOps and cloud security frameworks that enable faster innovation without compromising cybersecurity.
Our services include:
-
DevSecOps implementation and consulting
-
CI/CD pipeline security integration
-
Cloud security assessments
-
Infrastructure as Code security reviews
-
Container and Kubernetes security
-
Compliance and risk management
Our experts help businesses build secure, scalable, and compliant cloud infrastructure environments.
Conclusion
As cloud adoption and software delivery speeds increase, integrating security into DevOps workflows has become essential. DevSecOps enables organizations to build secure cloud infrastructure, automate security testing, and maintain compliance throughout the development lifecycle.
By embedding security into CI/CD pipelines, container environments, and cloud infrastructure, DevOps teams can detect vulnerabilities earlier, reduce cyber risks, and accelerate secure digital transformation.
Organizations that adopt DevSecOps practices are better positioned to deliver innovative applications while maintaining strong cybersecurity and compliance standards.
Category: Cloud management